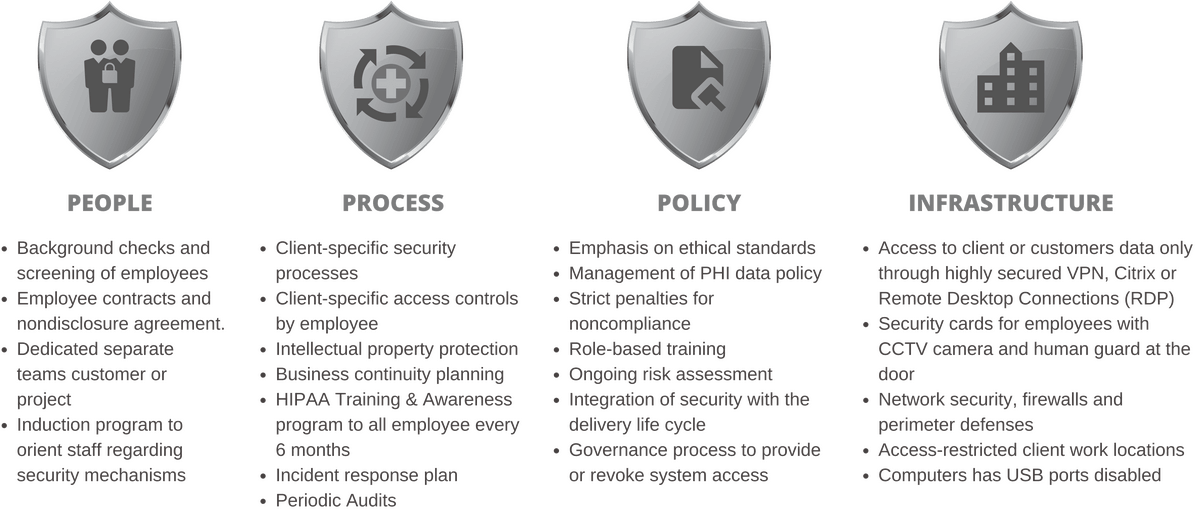
At Santeware, We are committed to respecting your data privacy and concerns relating to product security. We also understand the importance of appropriate protection and management of any PHI (Protected Health Information) you might share with us. We have established this Privacy and Security Policy so that you can understand the care with which we intend to treat PHI/ Product/ Process insights. All of healthcare is heavily influenced by three letters–PHI (protected health information). For obvious reasons, the exchange of PHI is heavily regulated in an attempt to keep individual privacy intact and prevent harmful actors. Understanding compliance requirements and implementing best practices is step one to any healthcare integration strategy.
At the most basic level, you must ensure 256 bit AES encryption of all databases and enforce HTTPS at an endpoint layer. If your solution requires VPNs, you must enforce IPsec protocol to ensure all traffic within the VPN is encrypted and authenticated. Finally, you must have business processes in place that outline response and notification strategies in the event of a breach.